- Cyber Dose
- Posts
- Think the Web History Is Gone?
Think the Web History Is Gone?
A Lesser-Known Browser Database That Contain Visited URLs

Happy you’ve joined the family here! I’m Husam, and this is where I share a light dose on cybersecurity, digital forensics, projects I am working on, and interesting findings from my work.
Want more? Check out my socials below:
Some updates if you do not already know:
I made 4n6Img website, where I gather forensic images to be the go-to database of verified forensic images to practice & research. Lots of new images coming!
I made IamHacked website, where I can help non-technical people to investigate & recover their social media accounts and computers if they got compromised.
I’ll be presenting Hidden Traces of Deleted Web Activity at the MSAB Summit 2026 on March 11, 2026, at 9:05 AM EST. Don’t miss it!
Now, let’s get into the main topic!
Many people may actually wonder what I would actually provide in my presentation @MSAB. There, I will be talking about some artifacts and methods to know users’ web activities even if the main browsers’ related DB were not available such as History, Places.sqlite, formhistory, etc. depending on the browser.
However, there are many other artifacts that could potentially show some related web data for users. For example, Permissions.sqlite
Yes, many people do not know about it, but I would consider it as a secondary browser’s history file!
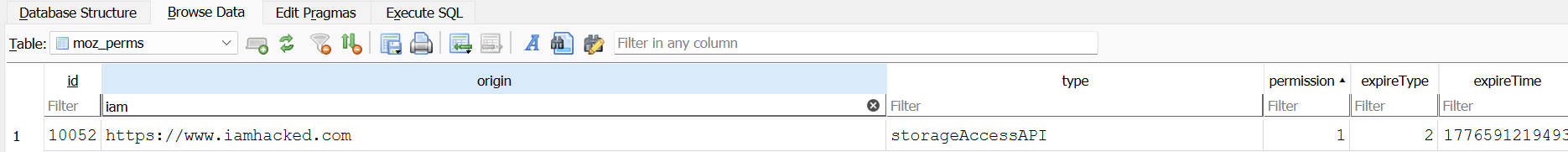
While exploring browser artifacts, I discovered a database that records the permissions websites request from users when they visit them.
Such permissions were:
StorageAccessAPI
Popup
Microphone
Camera
So, for example, when I want to use the web application of Teams to join a meeting, it will register microphone and camera permissions, and leave a trace on the Permissions.sqlite. Is not that amazing?!
This gives a glance what a user could have actually visited and there are also some indicators about extensions’ usage as well!
I found this database in Gecko-based browsers like in FireFox for my case. The database’s path found here:
C:\Users\[user]\AppData\Roaming\Mozilla\Firefox\Profiles\xxxxxxxx.default-releaseThe important table inside this DB is moz_perms, where the Origin column contains the visited URL or extension used and the Type column is the requested permission.
This is just a one small point in one of my slide in my upcoming presentation at MSAB, so stay tuned ^.^
Cya till the next time ~Hoxed
Do not forget to add this email ID to the whitelist, to not be received in the spam folder and miss the future issues!
Thanks for reading CyberDose! Subscribe to receive new posts and support my work.

I can help you further with:
1️⃣ Cybersecurity Investigation Projects
2️⃣ Digital Forensic Coaching
3️⃣ LinkedIn Cybersecurity Companies Branding
Click here, so we can talk!
Training Providers’ Partner Links
Here are some amazing partners’ platforms to learn from, click on the one you are mostly interested in:
Note: These are affiliate links to companies I work with and I believe their content would be valuable to you. Using them helps support my content.




Reply